But, there's an ingenious tool called AntiHookExec, which runs a specified program with all the hooks removed. AntiHookExec tries to find out the API hooks present in the system and if it finds any, then it "restores" the original APIs. So, the program which is started from AntiHookExec will not be affected by the API hooks of the Rootkit. AntiHookExec is an easy to use command line tool. The syntax is as shown below:
AntiHookExec ProgramName
where ProgramName is the name of the program (with its path) which needs to be started through AntiHookExec.
For example, to start Windows Task Manager through AnitHookExec, the command would be:
AntiHookExec Taskmgr.exe
Similarly, to start HijackThis through AntiHookExec, the command would be:
AntiHookExec C:\HJT\HijackThis.exe
assuming that HijackThis.exe is present in the folder C:\HJT\.
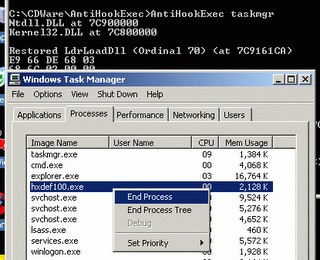
Below screenshots show the HackerDefender Rootkit's process and files visible in Windows Task Manager and Agent Ransack, a search tool, both of which started through AntiHookExec.













0 comments:
Post a Comment