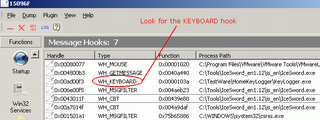
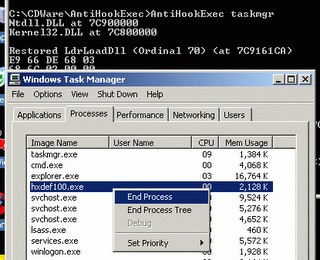
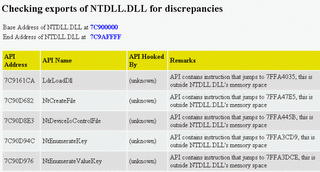
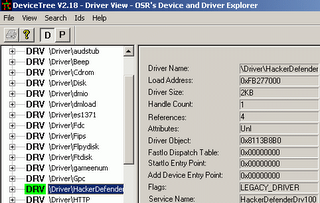
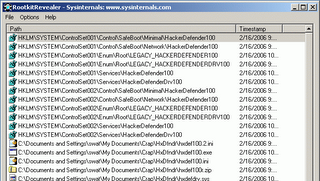
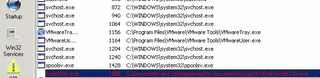
Gromozon is a new rootkit in the block. It installs a spyware called LinkOptimizer, giving the rootkit power to the spyware. Gromozon is a user mode rootkit and uses the AppInit_DLLs Registry key to load its DLL into memory. Moreover it hides this Registry key and hence it can not be viewed by "normal" tools like Regedit or HijackThis. Along with this, it also uses a host of other techniques like - randomly named DLLs, using Windows reserved names, hiding as ADS in NTFS systems etc. The DLL registered in the AppInit_DLLs key is responsible for the rootkit like behavior of Gromozon. It hooks some APIs in Kernel32.dll, Advapi32.dll, Psapi.dll and Ntdll.dll, to hide its files.
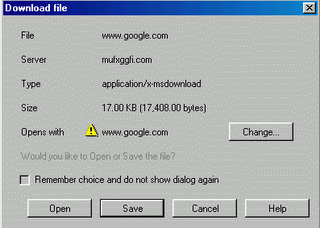
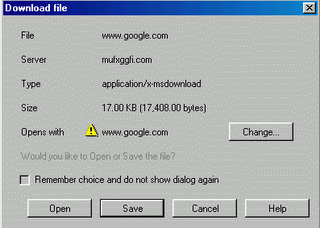
Gromozon tries to drops its file through a JavaScript. Most of the times, it drops a file named www.google.com. Note that, the file is not a HTML web-link, instead it’s an executable file with .COM extension! When this file downloaded, it downloads more malware components and installs into the PC. Here's a screenshot showing the Gromozon trying to drop its installer.
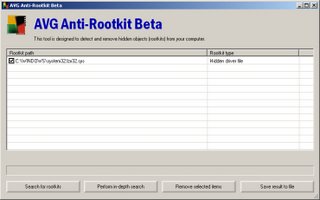
Prevx has released a removal tool which successfully detects and removes the Gromozon rootkit. You can download it here.
More information regarding the Gromozon can be obtained at CastleCops Wiki and in this excellent PDF document by Prevx researcher Marco Guiliani.
Gromozon tries to drops its file through a JavaScript. Most of the times, it drops a file named www.google.com. Note that, the file is not a HTML web-link, instead it’s an executable file with .COM extension! When this file downloaded, it downloads more malware components and installs into the PC. Here's a screenshot showing the Gromozon trying to drop its installer.
Prevx has released a removal tool which successfully detects and removes the Gromozon rootkit. You can download it here.
More information regarding the Gromozon can be obtained at CastleCops Wiki and in this excellent PDF document by Prevx researcher Marco Guiliani.