Message passing is a technique used in operating system for inter-process communications. In Windows, there are some standard messages and these are named WM_XXXX, where WM stands for Windows Message and XXXX is the actual name of the message. A complete list of messages and their description can be found in this page.
Message hooking is a technique in which a message is monitored (popularly called as hooked) by a program. Because of this hook, the hooking program gets a notification whenever that message is passed. Windows provides some APIs (functions) to hook messages, such as SetWindowsHookEx. Using this API, a message hook can be installed. Similar to the messages, Windows also provides various message hooks. These message hooks are named WH_XXXX. For example, a keyboard message has the name WM_KEYBOARD and the keyboard hook has the name WH_KEYBOARD.
Now a bit about keyloggers! There are two types of software keyloggers, namely DLL based keyloggers and driver based keyloggers. DLL based keyloggers, also called as hook based keyloggers, use the keyboard message hook to intercept the communication and capture key presses. They are named DLL based keyloggers because they use a DLL to to do implement logging functions. Driver based keyloggers are also called as Kernel level keyloggers. They use a device driver to directly monitor the keyboard, at kernel level, for key presses. Most of these keyloggers will not have any additional DLLs or executables. Only a driver is enough to do the job!
We can use IceSword to capture DLL based keyloggers easily. IceSword has a section named "Message Hooks" where it displays all the message hooks in the system along with the hooking program. There can be some hooks used by legitimate processes (for example, firewall, antivirus and even IceSword). But as we have seen earlier, keyloggers use the WH_KEYBOARD hook to hook the WM_KEYBOARD messages.
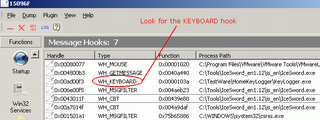
So, in this section of IceSword, just look for the WH_KEYBOARD hook. If this hook is present, note the process associated with it. In this example, we can see a process named Keylogger.exe is using WH_KEYBOARD. In this case, the process name is pretty straight forward. If you are not sure what really the hooking process is, just use Google to find information about the file. If there are no reliable information about that particular file, then upload and scan the file at any of the online file scanner sites (like VirusTotal or Jotti's Malware Scan). If the file is found to be "bad", then it should be removed immediately. IceSword's "Process" section can be used to locate and terminate the keylogger process. Once the process is killed, just navigate to the file location in Windows Explorer and delete the files.
The advantage of using IceSword to catch the keyloggers is that, it can show even "rooted" keyloggers, i.e. IceSword can detect message hooks even if, say, keylogger uses rootkit technology to hide. There may be additional files, related to the keylogger, in the system. Hence it is advised to update all the security software and do a full system-scan.
Since driver based keyloggers don't use Message hooks, they are not displayed in the "Message Hooks" section of IceSword. As we have seen earlier, these types of keyloggers use a device driver. Actually, this driver can also be detected using the "Kernel Modules" section of IceSword. But, in a system there will be large number of drivers, and it may become very tedious to go through the driver list shown by IceSword.
Download IceSword 1.18 English Version from here
Message hooking is a technique in which a message is monitored (popularly called as hooked) by a program. Because of this hook, the hooking program gets a notification whenever that message is passed. Windows provides some APIs (functions) to hook messages, such as SetWindowsHookEx. Using this API, a message hook can be installed. Similar to the messages, Windows also provides various message hooks. These message hooks are named WH_XXXX. For example, a keyboard message has the name WM_KEYBOARD and the keyboard hook has the name WH_KEYBOARD.
Now a bit about keyloggers! There are two types of software keyloggers, namely DLL based keyloggers and driver based keyloggers. DLL based keyloggers, also called as hook based keyloggers, use the keyboard message hook to intercept the communication and capture key presses. They are named DLL based keyloggers because they use a DLL to to do implement logging functions. Driver based keyloggers are also called as Kernel level keyloggers. They use a device driver to directly monitor the keyboard, at kernel level, for key presses. Most of these keyloggers will not have any additional DLLs or executables. Only a driver is enough to do the job!
We can use IceSword to capture DLL based keyloggers easily. IceSword has a section named "Message Hooks" where it displays all the message hooks in the system along with the hooking program. There can be some hooks used by legitimate processes (for example, firewall, antivirus and even IceSword). But as we have seen earlier, keyloggers use the WH_KEYBOARD hook to hook the WM_KEYBOARD messages.
So, in this section of IceSword, just look for the WH_KEYBOARD hook. If this hook is present, note the process associated with it. In this example, we can see a process named Keylogger.exe is using WH_KEYBOARD. In this case, the process name is pretty straight forward. If you are not sure what really the hooking process is, just use Google to find information about the file. If there are no reliable information about that particular file, then upload and scan the file at any of the online file scanner sites (like VirusTotal or Jotti's Malware Scan). If the file is found to be "bad", then it should be removed immediately. IceSword's "Process" section can be used to locate and terminate the keylogger process. Once the process is killed, just navigate to the file location in Windows Explorer and delete the files.
The advantage of using IceSword to catch the keyloggers is that, it can show even "rooted" keyloggers, i.e. IceSword can detect message hooks even if, say, keylogger uses rootkit technology to hide. There may be additional files, related to the keylogger, in the system. Hence it is advised to update all the security software and do a full system-scan.
Since driver based keyloggers don't use Message hooks, they are not displayed in the "Message Hooks" section of IceSword. As we have seen earlier, these types of keyloggers use a device driver. Actually, this driver can also be detected using the "Kernel Modules" section of IceSword. But, in a system there will be large number of drivers, and it may become very tedious to go through the driver list shown by IceSword.
Download IceSword 1.18 English Version from here











